Schmidt Happens
Wendy M. Grossman responds to "loopy" statements made by Google Executive Chairman Eric Schmidt in regards to censorship and encryption.

Google executive chairman Eric Schmidt has been making headlines again with a pair of loopy statements one hopes he chose out of a desire to be provocative rather than out of ignorance. First, he predicts that we may be able to end censorship within ten years. Second, he suggests that, "the solution to government surveillance is to encrypt everyone".
Oy. ...Let's take the last of these first.
"Mathematics is not your friend" Bruce Sterling declared in a wrap-up speech at the Computers, Freedom, and Privacy conference in 1994. At the time, it was not an overly popular message. The room was filled with people who passionately believed that freeing crypto from constraints on deployment and export was the key to privacy and security on the Internet. There were also comparisons to guns: as the argument goes, the Second Amendment is intended to ensure that the balance of power between citizens and the State is always somewhat equitable.
Granted, in the intervening (nearly) 20 years, encryption has not spread as widely as the cypherpunks had hoped. Only a tiny minority go to the trouble of encrypting email - but nonetheless you likely use encryption every day in forms that are invisible to you: every time you access a Web site via HTPPS, every time you buy something and SSL protects your credit card details in transit, and every time you make a phone call over a mobile network.
And what has happened? The security services have, as we've been reading since June, gone all out to break, undermine, or bypass the encryption. And - as Sophos' Graham Cluley writes - UK prime minister David Cameron is praising them for it. Moreover, he wants them to do more of it to penetrate the so-called "Dark Web".
Sterling was right: mathematics has not been our friend, and for a very simple reason. No matter how powerful the encryption used to protect data in storage or transit, at some point it has to be removed so that the people using that data at either end can view and work on it. As Caspar Bowden has explained in his careful work analyzing the vulnerability of non-US cloud systems to the US's FISA, FISAA, and PATRIOT laws, we are talking here about surveillance-as-a-service. We're talking hardwired back doors and permanent taps at key points, in which case, as I wrote in July, "interception is no longer a useful concept, and encryption is no longer a useful defense".
Adi Shamir, the "S" in the most widely used public key cryptography algorithm, RSA, has often said that you don't bother trying to crack the crypto, you just go around it. In a talk he gave in March, Shamir argued that crypto is becoming less and less of a useful defense. His example was advanced persistent threats, which hide out inside networked systems picking off tiny but valuable items of information to exfiltrate to the mother ship, but his comments apply as aptly to NSA taps, for the same reason. There is always a moment when the data is in clear text, and that's your target. I cannot believe that the former CEO of Google would not know this.
The ending censorship claim is sadly equally laughable. Censorship did not arrive with the Internet; it's probably as old as cave paintings. It's been known in all sorts of human cultures from China in 300 A.D. to medieval Europe. In his latest book, 'Writing on the Wall', in the process of exploring historical analogues to modern social networks, Tom Standage discusses historical censorship in pre-Revolutionary France and 17th century London.
Either Schmidt knows nothing of history or he's just being provocative and media-friendly (at which he obviously succeeded).
Censorship is in the eye of the beholder. Presumably Schmidt does not view Google's various efforts to block access to child abuse images, videos of crimes, and, under court order, torrent sites as "censorship". This despite the fact that, as Cluley wrote, saving me the effort, the former head of the Child Exploitation and Online Protection Centre Jim Gamble has told the BBC, search engines aren't how pedophiles search for these images.
Getting the search engines to do these things will make very little difference in terms of protecting real children from actual abuse. It's child protection theater, and it's being implemented under the same kinds of threats that were made against ISP in 1996 when they argued that blocking access to 133 Usenet newsgroups would be similarly ineffective. Indeed, these were the same threats that drove the creation of the Internet Watch Foundation.
Perhaps Schmidt thinks that censorship is the content blocking that other countries do. People who aren't us. Which we can fix, despite millennia of human history. As George Costanza said in Seinfeld when Jerry explains that he and Elaine have come up with a set of rules to allow them to remain friends while having sex on the side: "where do you get the ego?"
Wendy M. Grossman’s Website has an extensive archive of her books, articles, and music, and an archive of earlier columns in this series. Stories about the border wars between cyberspace and real life are posted occasionally during the week at the net.wars Pinboard or follow on Twitter.
Image: Eric Schmidt by Charles Haynes via Flickr (CC BY-SA 2.0)
Making CryptoParties Inclusive
CryptoParties are sometimes criticised for being a "geeks in black t-shirts only" event. In response, Milena Popova offers her perspective on how to make CryptoParty events more inclusive.

The CryptoParty movement, kicked off by Australian activist @Asher_Wolf over a year ago, intends to help people with any level of technical knowledge acquire useful skills to protect their privacy in the digital world. The 350-page, crowd-sourced handbook includes, among others, sections on browsing the web safely, securing your email, using disk encryption and secure telephony. Explanations progress from the basic (Don's use personal details in your passwords; make sure no one's looking over your shoulder when you're typing in your password) to the rather more advanced instructions for using email encryption on your phone.
One of the criticisms commonly levelled against privacy and security technology is its lack of usability. To use many of the technologies, you need a fair amount of skill and dedication, as well as the willingness to limit your platform choices and convenience at least to some extent. Personally, I am reasonably tech-savvy, but every one of my three attempts to start using anonymisation package TOR has ended in miserable failure. My need to access email easily and quickly on the go has so far trumped my need for security in my communications as the up-front investment to get anything sensible running across the multiple platforms I use has always seemed too high. In many ways, I and people like me are the prime targets of CryptoParties.
Of course, CryptoParties originated in a rather more innocent time, before the Snowden revelations, when to suggest that the kind of government surveillance we now know is happening was even possible would have earned you a tin-foil hat. With what we know today, the focus of CryptoParties and similar initiatives needs to shift. It is no longer only the reasonably tech-savvy and part-time conspiracy theorists like me who need to worry about the security of their communications - it is all of us.
It is good to see, therefore, that CryptoParties seem to be taking off in the UK. The Open Rights Group is doing its bit by supporting organisers, providing speakers, sharing materials and expertise. But what are we all doing to ensure that CryptoParties reach as wide and diverse an audience as possible?
When your event description is full of phrases like "full disk encryption", "password generation", and "keysigning", the general public may be forgiven for thinking this is a "geeks in black t-shirts only" event - no matter how many times you say that no prior knowledge is required. The language is immediately seemingly alienating. To attract people who need a basic introduction to online privacy the most, we may need a change of approach. We need to work out what it is that people are really worried about. We need to understand our user stories, and promote CryptoParty events in a way that addresses them.
Let me give you some examples...
Lori is a food blogger worried about a rise in the number of food banks. She is also a single mum with a three-year-old daughter. She has some influence in the food blogging community now; has published a Comment is Free piece or two and is starting to get her first rape threats on Twitter. She wants to ensure her and her daughter's physical safety. Things that might convince Lori that attending a CryptoParty would be useful for her include a focus on personal safety - and maybe some activities for children so she can bring her daughter along. Indeed, the upcoming Brighton CryptoFestival is offering a range of kids' activities - big thumbs-up to them!
Liam is an accountant in his mid-30s. One of his friends recently lost his job because his boss found lots of pictures of him drunk on Facebook. Liam's worried about who can see the things he posts on Facebook. Some words around social media safety and privacy might help Liam decide to come to your CryptoParty.
Jack is unemployed and on benefits. He accesses his Gmail at the local library and uses that to manage sensitive data like job applications. He also accesses social media, newspaper websites, the JobCentre website, etc. Jack might not even know that someone using the computer after him could potentially access his CV, his search and browser history, or his social media accounts. Jack might come to a CryptoParty if we include some activities around safety on shared computers and networks - and explain up front why this is important. The fact that your event is free and advertised as such will definitely be important to Jack.
Another example: Ellen needed to hire a ladder a few weeks ago for some decorating work in her new shop, so she googled "ladder hire". Practically every website she's visited since then has had ads for ladder hire. She's beginning to suspect this is not some kind of freaky coincidence. Include some activities on tracking, what companies like Google know about you, and safer web browsing to entice Ellen to join your CryptoParty.
Of course, to some extent the kinds of activities you'll be able to offer at a CryptoParty will depend on who you've got available to share skills and teach. Having said that, it is often the more basic topics - like Facebook privacy and helping people install Ghostery on their browser - that will have the biggest appeal to the general public and the most immediate impact on individuals' privacy. Keep that in mind with planning and promoting your event, and you'll make a bigger impact.
Milena Popova is an economics & politics graduate, an IT manager and active campaigner for digital rights, electoral reform and women's rights. She is also a member of ORG's board and continues to write for the ORGzine in a personal capacity.
A Look Back At Autumn
As his internship at the Open Rights Group draws to an end, Patrick Ireland looks at some of the best articles published during October and November.

It's been a difficult couple of months. Since leaving university, combined with an untimely breakup and a rather depressing visit to Thailand, life has been coloured in a kind of gloomy greyish melancholy. Like most graduates I have been tasked with the somewhat daunting prospect of 'carving out a place in the world'. And believe me - after the 'bubble' that is university - this has proved challenging at the best of times.
However, almost two months ago I was lucky enough to be offered an internship at the Open Rights Group working on the zine. Although my understanding of digital rights issues were limited (as was my understanding of technology in general) I was excited to join an organisation fighting a war on all fronts against increasingly intrusive states and corporations. I am often guilty of romanticism and whimsy - but working for ORG did feel like I was fighting the 'good fight'. Or at least I was surrounded by people fighting it. At times I imagined that, if this were the 1960s, I would be brushing shoulders with some of the revolutionaries and activists described in Christopher Hitchen's excellent memoir Hitch 22. The modern revolutionaries perhaps? ;)
Regardless, as the various articles I have published during my time at ORG proves, this is an important fight.
Some of the highlights from the zine in the last two months include:
* Milena Popova's article on the changes to Google's Terms of Service. After reading the article I immediately e-mailed her saying "I'm afraid of Google". Her response was simply "you should be". I think what disturbs me the most about these corporations is their ugly view of humanity: we are merely 'consumers' to them. Such cynicism is probably more dangerous than some of us might suspect and history has repeatedly taught us that dehumanising people in such a way never yields a positive outcome.
* Matteo Bergamini - the Founder and Executive Director of Shout Out UK - offered a nice perspective on the rise of citizen journalism. He called journalists the "unsung heroes of the people" and this appears to almost certainly be the case in light of recent events. Newspapers like The Guardian have acted heroically in their reports surrounding PRISM and the NSA. We not only owe Edward Snowden a great debt - but the journalists who were brave enough to publish the material he uncovered.
* Wendy M Grossman's piece on surveillance was another highlight - the worrying fact that many of us feel safer knowing that we're being watched or spied upon. Protecting us from terrorists, eh? Maybe. My conclusion, Orwell's 1984 should be made compulsory reading in schools.
* Other great articles explored David Cameron's controversial porn filter and the problems with short-termism in digital policy debates.
* I also very much enjoyed writing about Russell Brand and the controversy surrounding his attack on the political establishment. Is a revolution on the horizon? I don't think so. But change is coming - as the reaction on the web and social media seems to suggest.
So that's it for October and November. Of course, there have been many great articles and I sadly can't write about them all. I would like to thank ORG for giving me the opportunity to work on the zine... the bubble may've burst, but there is life after uni.
Patrick Ireland is currently doing an internship at the Open Rights Group. He is also a Correspondent for the digital newspaper Shout Out UK and hopes to attend the London Film School in January 2014 to pursue MA Filmmaking.
Image: Che Guevara mural, Havana, Cuba by Andy Watson-Smith via Flickr (CC BY-NC-ND 2.0)
Content is King
Wendy M. Grossman takes a look at two big stories this week that both deal primarily with content and its owners.
Two big stories this week, both, in their separate ways, about content and its owners.
The first was the final despatch of the Google Books lawsuit by judge Denny Chin of the United States Court of Appeals for the Second Circuit. This thing has been percolating since 2005, a year after Google started its scanning project; the history is probably best explained in this 2011 article by Pamela Samuelson (PDF). Briefly, Google got sued, first by publishers and then by authors; and settlements of the lawsuits were rejected on all sorts of grounds. Now, the last of these has been dismissed - a judgment that has been widely welcomed as a win for fair use and innovation: by Wired, the Washington Post, the New York Times, the Guardian and digital libraries expert Karen Coyle.
The Authors Guild plans to appeal, but I'd suggest they try asking their members first how many of them actually use Google Books. I bet the answer will be: lots, just like Judge Chin's law clerks. I'd like to see alternatives (because I would like to stick to the terms of my 2010 divorce from Google, but the fact is it's damn useful to have a searchable repository that opens up access to work that otherwise increasingly might as well not exist. The best news about this decision really isn't the effect on Google; rather it's that by ruling that scanning books and allowing searches to return small chunks of their contents is fair use the court has opened the way for others to do the same thing. You may argue that very few others have Google's resources, but that doesn't have to stay true: Wikipedia, Open Street Map, and Open Corporates have all shown what can be done with collaborative hard work; why not Open Books?
Coyle, who makes the point that libraries have played a vital role in securing this judgment (the judge in the case frequently cites the American Library Association's amicus brief (PDF), welcomes the ruling as "an opportunity to rethink digital scholarship based on materials produced before information was in digital form." What she does call for, however, is a project to correcting the OCR errors in those scans.
The second big story of the week is, of course, the release of the text of the copyright chapter of the draft Trans-Pacific Partnership treaty, which until now has been kept secret. The guts of the actual provisions have already been helpfully analyzed; see for example Dan Gillmor in the Guardian, Canadian legal scholar Michael Geist, and James Love at Knowledge Ecology International, who calls it "bad for access to knowledge, bad for access to medicine, and profoundly bad for innovation".
What's clear, since the leaked chapter includes the detail of which country is pushing for which provision, is that the US is taking the lead in trying to expand intellectual property rights and shrink the exceptions to them. In Geist's analysis, he notes that his country is often one of the lead opponents. Which in turn means that the interests of ordinary Americans, as opposed to rightsholders, are being better protected by Canada than by the US government we actually pay to do it.
Love also writes eloquently about the many problems surrounding the secrecy of the negotiations - secrecy that extends even to much of the US Congress.
This is one time when it's absolutely clear that the negotiating parties cannot claim that they didn't know these provisions were contentious. There were – famously - street demonstrations to block the first attempt at getting these policies into international law, the SOPA and ACTA treaties. It wasn't just the improbability of people caring that much about what used to be such an obscure area of law – it was also that the demonstrations were in outdoors in mid-winter in places like Poland and Sweden.
But what matters even more than the reality is the principle. Even if TPP weren't a shady backroom effort to sneak the widely despised provisions of the deceased SOPA and ACTA into law, the secrecy would still be wrong. Even if you could make a reasonable case that there are parts of the treaty that are genuinely sensitive for security reasons, there is no possible way the copyright provisions are among them. But it is a shady backroom effort. The street demonstrations against ACTA must have left them in no doubt about its unpopularity. They can't say they didn't know how many people, experts, and organizations believe that expanding intellectual property rights is both morally and economically wrong.
What's that line that the security services and law enforcement are always telling us to justify installing privacy-invasive systems "for your safety"? Ah, yes: if you have nothing to hide, you have nothing to fear. Shouldn't this be more applicable to governments negotiating international treaties that are going to become domestic law than to ordinary citizens who just want to see their doctor in private?
Wendy M. Grossman’s Website has an extensive archive of her books, articles, and music, and an archive of earlier columns in this series. Stories about the border wars between cyberspace and real life are posted occasionally during the week at the net.wars Pinboard or follow on Twitter.
Unified Field: The 'Splinternet'
Is the 'Balkanizing of the Internet' - the notion that the web might break apart along nation-state or commercial boundaries - a genuine threat? Wendy M. Grossman investigates...
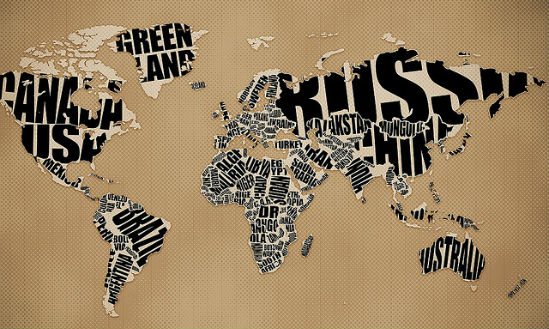
For as long as I can remember, the notion that the Internet might break apart along nation-state or commercial boundaries has been a threat. Usually called "Balkanizing the Internet", the "Splinternet", as Becky Hogge called it at the Cybersalon last week, has become a topic for discussion due to the Snowden revelations. To some people it doesn't sound so bad any more; to others it's still automatically doominous.
This week, Eva Pascoe (@cybersaln) sent out a query: was it likely? Would it be technical or political? And that's when I realized for the first time that, at least in its current form, it's a nonsense threat.
There are at least four different ways the Internet could be "Balkanized". The current usage derives from threats by Brazil and Germany (chiefly, but not solely) to pass national laws requiring data pertaining to their citizens to be stored locally instead of shipped around the Internet into the purview of the NSA. Folks like the vocal Lauren Weinstein call this both hypocritical (because the countries spy on their citizens themselves) and dangerous (because it would split the Net by raising barriers to the free flow of information).
But this particular sense is about private data storage, not flows of data meant to be published. There are myriad vast data stores on the world's computers that do not touch the Internet or do so in very restricted ways and it matters not at all. What difference does it make if the entity demanding local control over its users' data is Brazil or Facebook? I would argue: none – and storing data locally is likely also to aid network efficiency. Sure, the US doesn't like the EU's widely copied data protection laws because they impede the free trade in data from which US data-driven companies make so much money. But that doesn't mean the rest of us have to facilitate that. More important, as Caspar Bowden has been pointing out (PDF), local storage won't protect against NSA spying because US companies' foreign subsidiary are subject to FISA and the Patriot Act no matter where the data is stored.
The two original senses of "Balkanization" are more serious. The first is censorship. Twenty years ago, as now, there was much concern about attempts to regulate content at national borders. These would either turn the Internet into a patchwork of unpredictably unreliable access to information or a lowest-common-denominator medium hosting only the most universally acceptable (ie, blandest) content. Twenty years on, various countries do filter and censor, the Internet's somewhat porous quality has largely survived, even though some people can't access some types of information at some times from some locations.
The second was about the management of addressing, an issue of technical Internet governance overseen since 1998 by the Internet Corporation for Assigned Names and Numbers. Although there are many registrars selling domain names and many registries (one for each country and generic top-level domain), ultimately transforming human-friendly domain names into the numbers computers use is a monopoly distributed by 13 root servers. The feasibility and dangers of splitting the root have been the subject of many debates and disputes over the years. Snowden has revived the uneasiness outside the US about ICANN's remaining ties to the US Department of Commerce. The upshot is much more interest in other, more international governance efforts such as the Internet Governance Forum than there was six months ago. Still, what scares people about this is not so much Balkanization as that the participation of so many governments with conflicting regulatory agendas could stall the Internet's development entirely.
The final sense is the one network neutrality is meant to protect against. This would be the scenario in which access providers discriminate against traffic they don't like: the cable company that also owns TV stations and accordingly demands a very large ransom from Google and Microsoft to allow subscribers to access YouTube and Skype or slows down the connections to the point where those services are unusable. The answer to this is not allowing this sort of cross-ownership (a classic anti-trust issue) or, failing that, for regulators to insist that all types of traffic be treated equally. There's some delicacy surrounding how to phrase this so that it doesn't outlaw traffic-shaping, a legitimate tool for defending against certain kinds of attacks and for ensuring that you don't interrupt someone's video stream of live tennis at match point in order to deliver an email message whose recipient wouldn't notice a two-second delay. But delicately phrasing things is what lawyers and policy makers are for.
So, yes, all these threats have some potential to disrupt the Internet as we know it. Of the four, I'd say the local data aspect is more interest-group hype than real threat The bigger threats are structural censorship and the loss of network neutrality, both of which could play into the hands of large, commercial interests who would prefer to turn the Internet into a captured broadcast medium cum giant data collection platform. Whether local data storage can be meaningfully forced on a network that was specifically designed to connect people regardless of nationality or location is an entirely different matter.
Wendy M. Grossman’s Website has an extensive archive of her books, articles, and music, and an archive of earlier columns in this series. Stories about the border wars between cyberspace and real life are posted occasionally during the week at the net.wars Pinboard or follow on Twitter.
Kickstarter: Liquidity Issue or Greed?
Corwin Bex takes a look at some of the recent funding problems in-development games are facing on Kickstarter.

Kickstarter is reported to have received $825 million in funding since its launch in 2009. The idea of Kickstarter is to provide a place to propose ideas to its millions of members and then receive financial backing in return for rewards depending on 'Pledge' sizes. Kickstarter benefits from this as it receives a 5% cut and Amazon receives 3-5% for processing the transactions.
But let's talk games, specifically games on Kickstarter. Many games have been successful in reaching funding via Kickstarter – from thousand dollar games to million dollar games. That said, with most of these games only reaching Kickstarter by 2012, it is extremely hard to analyse the apparent success rate of Kickstarter. What can be said however, is that financial issues have been widespread despite - and in some cases - the games actually being over-funded.
It would be extremely foolish to ignore the 'elephant in the room' example, that of Double Fine's 'Broken Age'. The initial project was asking for $400,000 to make a point and click adventure game, a game style that has been neglected in recent years and, as a result, Shafer argued that publishers would be uninterested in funding; ergo why Kickstarter.
So why after a extremely successful Kickstarter campaign (reaching $3.3million in 'Pledges') has the game recently and extremely publicly ran into liquidity issues?
It would appear that Shafer and Kickstarter made a grand mistake in attempting to overgrow the original idea far beyond a $400,000 game. Sadly, it seems to have grown too far. With almost a year left in development they announced via their monthly documentary (part of the reward for backing the project) that the project was short by almost $3million. As such, Shafer has been forced to pre-sell the game by releasing half early on Steam in hopes that this income can supplement the cost of the rest. This will in all probability fail due to the likelihood that the majority of players of this type of game would have already bought the game via the initial Kickstarter.
But this failure is tiny in comparison to other projects that have actually been 100% cancelled due to money issues. 'The Doom That Came To Atlantic City' - a monopoly inspired board game recently announced a complete cancellation of the game despite being over-funded with $122,874 compared to the initial £35,000 goal.
'CLANG' is another project that has been cancelled due to money issues. This project's biggest issue was its reliance on having a secondary accessory used for the actual sword fighting (think Wii sword fighting). Indeed, they actually ended up making a second Kickstarter for this accessory. The project ultimately raised $526,125 of its $500,000 goal – yet announced to be out of money within a year. Worryingly, the second Kickstarter for the accessory received $650,000 of funding of its $250,000 goal.
When Professor Ethan Mollick looked into Kickstarter he found that "75% of companies deliver products later than promised" from data samples of 47,000 Kickstarter projects amounting to $198million in contributions. The idea of caution can only be cited and it is again worth noting that Kickstarter is backing a project and not pre-ordering a product like many believe.
But this also raises another significant question: do they really need your money? Plenty of successful Kickstarters have amassed large personal fortunes... so shouldn't they just self-fund?
'Shroud of the Avatar' by Richard Garriott received $1.9million in funding for a RPG game; the focus of the campaign was on Richard Garriott – even using his nickname 'Lord British' in the title of the game. However, Garriott could have very easily funded the game himself. In 2008 he spent a reported $30million going into space to the ISS.
Does Garriott really need Kickstarter? Or is he simply using it as a means of advertising the game, guaranteeing a mass amount of click traffic via PC Gamer and Gamespot before it is even released? Is this just a cynical opinion?
Peter Molyneux's 'GODUS' Kickstarter could be another example of this. His Kickstarter reached $526,563 in funding – yet Molyneux himself is an extremely wealthy individual following the success of the Fable series of games. Once again, I find myself asking if this is this yet another clever marketing tool?
Kickstarter is a great platform that provides completely unknown developers a platform to test an idea and hopefully get the funding to make it into a complete game without the personal risk. This not only benefits the gaming industry as a whole (more indie games and original ideas), but it also benefits gamers themselves. Kickstarter provides the means to have a direct input into the game. Simply put, Kickstarter puts the 'Backers' in charge.
The issues from Kickstarter are always going to receive much more media attention than any of the smaller successful projects (see FTL). So please dear reader, go look on Kickstarter, experience its potential, and maybe back a few small indie games. Not just the big hits.
Corwin Bex, BA Hons History, avid PC Gamer, and writer of all things tech and game related.
Image: Kickstarter Support Logo by amytrippmyers via Flickr (CC BY-SA 2.0)
The Revolution Starts Here: Can the Internet Change Politics?
Russell Brand calls for a revolution and the web responds. Patrick Ireland explores whether the emergence of the internet and social media has made revolutionary political change more feasible.

Comedian. Actor. Libertine. Political Activist. And now apparently 'guest editor' of the New Statesman. Just to give you some facts and figures: over 10 million people watched his interview on the BBC's Newsnight and a record 2.68 million unique users visited newstatesman.com during his stint as editor. Like him or not, it would be hard to describe Russell Brand as either 'dishonest' or 'false'. Indeed, it is arguably his sincerity that makes him such an attractive celebrity icon. And personal politics aside, it is clear that he has captured the public imagination in some shape or form.
But we are not here to discuss the legitimacy or truth behind Russell Brand's political beliefs. The reaction on the web and social media raises a rather significant question: can radical political change (or a 'socialist revolution' for example) be ignited or potentially organised through the internet and the use of social media? Have recent advances in technology really changed the political game?
On Facebook there is already a growing number of users calling for Russell Brand to be elected Prime Minister (or “chief admin bod” in his own words). This suggests, regardless of whether they are serious or not, that radical – one could almost say 'revolutionary' – political change is on a great many people's minds. Moreover, Brand has over 7,000,000 followers on Twitter. To put that into perspective; Pope Francis has just over 3,000,000 and David Cameron sits on barely 500,000.
I spoke briefly to Professor Ian Grigg-Spall - a former lecturer at the University of Kent and currently the Academic Chair of the National Critical Lawyers' Group - in search of answers. He said that the internet and electronic communication could obviously help "organise revolutionaries and transmit their message to the public". He pointed to various cases of social media being used to help organise and support so-called 'revolutionaries' - the current political instability in Egypt being a prominent example. "Did Facebook and Twitter cause the [Egyptian] revolution? No. But these tools did speed up the process by helping to organize the revolutionaries, transmit their message to the world and galvanize international support". Even the anti-austerity protests in the UK (most recently the 'Bonfire of Austerity' in Parliament Square) are largely organised and coordinated through the use of social media.
On a much darker note, Grigg-Spall did note that the internet can be "a double edged sword". Why? Because the state can "take these tools away" - just as it did in Egypt by suspending Facebook and Twitter. "Revolutionaries cannot rely on the internet alone" he concluded.
Of course, this may scare some - or bring an inkling of hope to others - but Karl Marx continuously claimed that a socialist revolution could not be achieved until capitalism developed the 'means of production' to a certain point. In other words, capitalism was a kind of 'necessary evil' before the transition into socialism because it allowed technology to rapidly grow and advance. This would, as a consequence, make social and economic equality under socialism much more feasible. Furthermore, the concept of a global revolution (one of the main pillars of Marxism) becomes arguably more tangible in light of the internet. We are all connected now and this opens up a new range of possibilities.
Scared yet? Or maybe you're just about to burst into the opening lyrics of L'Internationale?
Ultimately, Russell Brand is not afraid to speak his mind. I suppose he's the epitome of political free speech. He is not afraid to say that our leaders have failed us. That western democracy has been replaced by a corporate plutocracy. That our very political system is both inherently flawed and completely indifferent to the suffering and struggles of normal people. That we can do better for our planet and it's people - many of whom are desperately poor and miserable. Bottom line: capitalism – or perhaps 'neoliberal capitalism' for those who can't bare to comprehend that the whole thing is 'damaged goods' – has failed and is currently propelling us to our own bloody destruction. According to Brand, the only thing that can stop our apparently apocalyptic future is revolution.
“Total revolution of consciousness and our entire social, political and economic system" writes Brand. "Is utopian revolution possible? The freethinking social architect Buckminster Fuller said humanity now faces a choice: oblivion or utopia”. I can't help but be reminded by the old leftist slogan in that last sentence... Socialism or Barbarism?
Patrick Ireland is currently doing an internship at the Open Rights Group. He is also a Correspondent for the digital newspaper Shout Out UK and hopes to attend the London Film School in January 2014 to pursue MA Filmmaking.
Image: Russell Brand by Esten Hurtle via Flickr (CC BY-NC-SA 2.0)
The Rise of Citizen Journalism
Matteo Bergamini, the Founder and Executive Director of Shout Out UK, writes about the rise of Citizen Journalism and the so-called 'Fifth Estate'.

Recent history has seen many changes. Our generation have witnessed the rise and fall of dictators, the rise of police states and the erosion of our civil liberties, economic war taking precedence over human casualties. Money, in the 21st century, has become more important than human life.
We have also seen the rise of whistleblowers and people ready to stand up against the machine that has warped our existence into to that of a soulless drone. The likes of the Occupy movement has challenged the very existence of the global capitalist system. International coalitions have made it their life’s work to protect the internet from the ever extending arm of government whilst whistleblowers have given up their entire lives for humanity and the little rights we still have and hold on to. We are in an age of change, for better or for worse. Yet where does journalism fit in?
Journalists, the unsung heroes of the people, have always delved to expose what governments refused to share with their people. Journalists have stepped up when the police have faltered and failed. One can find clear examples of both in the Watergate and Spygate scandals –and also in a show called ‘To Catch a Predator’ by Dateline; all examples of police work done by journalists.
So what about journalism in the 21st century...?
'Citizen Journalism', like it or not, is here to stay. We are in a digital age and almost everyone has a phone with a camera or a video recorder. In other words, everyone can be a journalist.
So-called 'citizen journalism' has given rise to direct live streaming of events. It allowed us to see the British government nearly raid the Ecuadorian embassy and in so doing breaking international law. Citizen journalists managed to cover the event hours before the mainstream media even got to the scene.
Citizen journalism has also given rise to direct, in the fray, coverage of protests from the front line. This has given us shocking and often terrifying accounts of immense police brutality in regards to protesters, removing the veil that once covered protest zones. An interesting example of this being the Occupy movement’s march on the New York stock exchange, which was shut down with incredible violence. An example closer to home can be taken from the eviction of the ‘Bank of Ideas’ from the old UBS HQ, which saw sow contracted private officials using immense violence to remove protesters.
Citizen journalism, to some, is a danger. These are often inexperienced journalists who may or may not be bias. Some even ask: ‘how can we trust them?"
It seems very humorous to see such remarks, as unless I am mistaken, the Sun, the Daily Mail, the Times and the Guardian are all very bias?
I would say the only difference between the established media and citizen journalism is that the bias in mainstream media is decided by one or two people, the owner and/or editor. In citizen journalism, the multitude of bias will bring to light the truth. Not to mention that citizen journalism does not have the financial capacity or the will to break many privacy laws simply to get slightly more intrusive celebrity news, something the News of the World did time and time again.
Citizen journalism and its rise have shown us many truths, otherwise gone missing or even omitted. It is bringing to light the grave issues the world is facing. I run a small news network called Shout Out UK, which aims to create an understanding between current affairs around the globe and the history behind each issue. It is our firm belief that the lack of historic context in current mainstream print media is the primary reason behind why many issues around the world seem 'unfix-able'. Any sites offering information and live coverage on current affairs exist and are only limited by your imagination and interest.
On the 10th October, the European Court of Human Rights issued a judgement in Delfi AS v. Estonia (no.64569/09), a case about the news portal’s liability for third-party comments made on its website. It’s a blow for free speech and shows how important the continuous growth of citizen journalism is. As individual government’s crack-down on renowned sites and established media continues, people will turn more and more to citizen journalists for the true side of events. Citizen journalists are becoming the bastions of free speech, as professional journalists were before them. Sociologist William Dutton from the Oxford Internet Institute (OII) argues that we are witnessing the emergence of powerful new voices and networks which can act independently of mainstream media. He has termed these developments the emergence of the ‘Fifth Estate':
'Highly networked individuals (helped by new platforms like social networking and messaging) can move across, undermine and go beyond the boundaries of existing institutions. This provides the basis for the pro-social networks that compose what I am calling the Fifth Estate'.
Anyone that has a camera is, has the right to be and has the duty to become a citizen journalist if he or she witnesses an event that should be exposed and voiced. Citizen journalism is everyone and no one. No more will ignorance fall on humanity about the tragedy in Iran or Sri-Lanka, no more can we as humans claim to not know about the atrocities in Russia or the USA. Indeed, the Arab Spring was so powerful partly due to citizen journalism and the global public support that it achieved for the Arab Spring.
Citizen journalism will grow strength in strength and as long as the internet remains free and accessible. It will continue to thrive and give people the information they need to have.
Matteo Bergamini is the Founder and Executive Director of Shout Out UK. He is currently studying Politics & History at Brunel University and is expected to graduate in 2014.
Image: Occupy Wall Street by David Shankbone via Flickr (CC BY 2.0)
[VIDEO] Edward Snowden: Whistleblowers in the Digital Era
Fransesca West (policy director of Public Concern at Work), Peter Tatchell (political activist), Malcolm Rifkind (Chairman of the Intelligence and Security Committee), Heather Brooke (investigative journalist) and David Omand (former GCHQ director) discuss their opinions about Edward Snowden and the debate around his leaks.

Image: Edward Snowden Painting by Thierry Ehrmann via Flickr (CC BY 2.0)
Innovation Under The US Government Shutdown
Patrick Goold explores some of the effects the recent US Government Shutdown had on Innovation Policy.

It can hardly have passed you by that between October 1st and October 16th, the US Government closed its doors. Congress, wrapped up in its ongoing struggle surrounding President Obama’s health care reforms, failed to enact legislation appropriating funds for the coming financial year and thus forced routine federal government operations to grind to an embarrassing halt. According to Standard and Poor this cost the US economy $24 billion in total. But what may have passed you by are the effects that the government shutdown had on innovation policy.
Most importantly, fundamental actors in the protection of intellectual property failed to carry out their usual duties. The Copyright Office closed. During the closure it continued to accept registrations for new literary and artistic works but delayed processing them until the reopening. The US Patents and Trademarks Office (USPTO) faired slightly better. Enough revenues had been earned from patent application fees in the prior year to keep the USPTO functioning. Yet this did not mean it was business as usual. At least one important public meeting on copyright reform, entitled “Copyright Policy, Creation, and Innovation in the Digital Economy,” was postponed from October to December citing “complications” arising from the shutdown. And the announcement made on October 1st stating that the USPTO would stay open made clear that the office only had enough funds for four weeks of government absence.
Both the International Trade Commission (ITC) and Federal Trade Commission (FTC) followed the Copyright Office into hiatus. The ITC exists in part to offer patent owners a fast and efficient relief against imports that infringe US patents. But during the shutdown this option was foreclosed to patentees, thus defeating the organization’s role in providing timely patent protection measures. Even now the ITC has reopened, the delays caused by the shutdown are likely to continue causing confusion, as many cases need to be rescheduled. Simultaneously the FTC’s research into non-practicing-entities, otherwise known as patent trolls, was stopped. We are still waiting on their report giving proposals on how to tackle the perceived troll problem.
Nor did the problems facing the IP system stop at the domestic level. The US Trade Representative (USTR) is currently negotiating the Transatlantic Trade and Investment Partnership. This international trade agreement between the EU and US will contain a number of provisions on intellectual property. As the USTR closed down, it had to cancel an important meeting in Brussels. Similarly President Obama cancelled his trip to Indonesia, where he was expected to take part in the Asia-Pacific Economic Consideration summit, which had scheduled discussions on another major trade agreement with intellectual property provisions, the Trans-Pacific Partnership.
Scientific research equally took a hit. The National Cancer Institute furloughed almost 80% of its workers, postponing many clinical trials. Patients could not enroll at the Centre for Disease Control or the Food and Drug Administration. While innovation in the energy market slowed as the Department of Energy’s leading research and technology development offices, including the Office of Science and the Office of Energy Efficiency and Renewable Energy, were run by skeleton crews. This dramatically reduced the number of people working on various clean energy projects.
The fascinating lawsuit between the tech companies and the US federal government in relation to the NSA was also unsurprisingly postponed. Various companies, including Microsoft, argue they have a right based on the First Amendment to reveal details related to NSA information requests.
It is perhaps no surprise by now that the short-term political interests can corrupt our long-term innovation goals. But usually this relationship is more insidious, hidden from the public. In 1998, the Copyright Term Extension Act added a full twenty years to the term of copyright protection, largely at the behest of Disney who wished to keep Mickey Mouse from falling into the public domain. The government shutdown highlights a new, less planned and more calamitous, way innovation can be sacrificed to the problems in our democratic system.
Of course if the US federal government cannot separate politics from innovation, perhaps some other entity can. When it was announced that the NASA website was to shut down, Russia’s Pirate Party came to international rescue. In an open letter to NASA, the party offered to host the website on its servers until the fiscal crisis was over. At least the offer was made with enthusiasm, ending as it did with the words “We love Mars”.
And while very few people would be happy with handing over the NASA website to Russian pirates, perhaps a lesson is still to be learned from their offer. When a nation acts like a child, others will treat it as one.
Patrick Goold is the Microsoft Research Fellow at University of California, Berkeley, School of Law. He holds an LL.B. from Newcastle University, an LL.M. from Cornell Law School, a PhD from the Max Planck Institute for Intellectual Property and Competition Law, and is qualified to practice law in New York. His research interests include intellectual property law, legal theory, and international law.
Latest Articles
Featured Article
Schmidt Happens

Wendy M. Grossman responds to "loopy" statements made by Google Executive Chairman Eric Schmidt in regards to censorship and encryption.
ORGZine: the Digital Rights magazine written for and by Open Rights Group supporters and engaged experts expressing their personal views
People who have written us are: campaigners, inventors, legal professionals , artists, writers, curators and publishers, technology experts, volunteers, think tanks, MPs, journalists and ORG supporters.